Why it matters: VLC is universally regarded as one of the best (if not the best) media players available today. A new version released a couple of days ago brings further improvements for the program’s compatibility, stability, security and format support.
VideoLAN, the non-profit organization promoting the power of open source to rock the multimedia world, has just released a new version of VLC media player. VLC 3.0.18 is the 19th update of the “Vetinari” codebase, and is a much needed one for both casual users and longtime fans of the program.
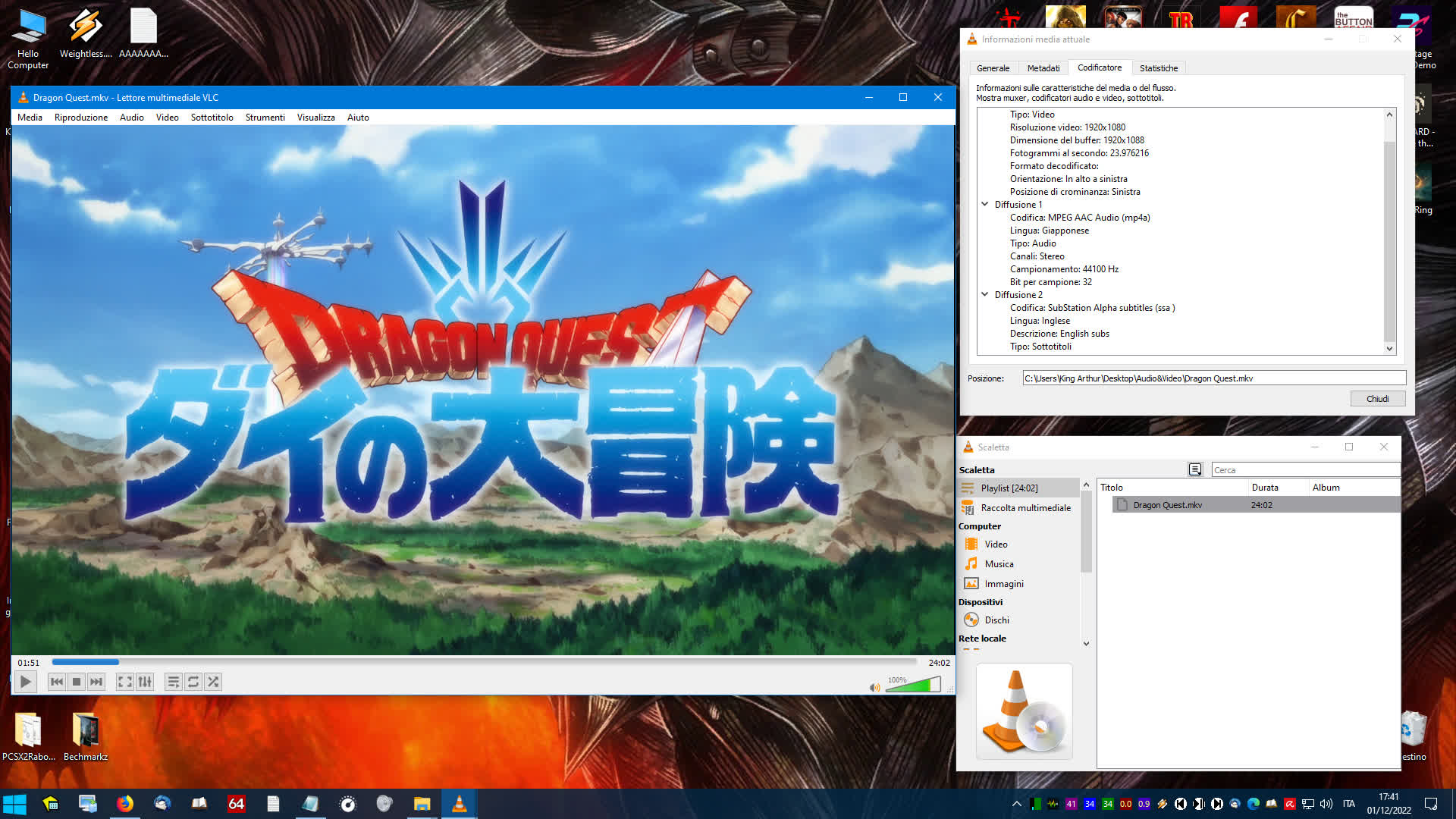
VLC media player 3.0.18 adds support for a few formats, improves adaptive streaming support, fixes some crashes and updates many third party libraries, VideoLAN said. The new media player fixes seeking for some media formats, improves file compatibility with older GPUs, and remedies select SMB protocol behaviors.
Furthermore, the update avoids a playlist live loop in case of only very tiny or failed items, solves “numerous” crash-related bugs and adds support for DVBSub inside MKV media files. The list of libraries and components that were updated includes FFmpeg – a suite which is essentially the beating heart of many media-related, open source projects – upnp, x265, libsmb2, dav1d, libass, zlib, GnuTLS, mpg123, and more.
VLC media player 3.0.18 also updates the library handling Blu-ray (unprotected/ decrypted) optical discs, finally solving one of the most longstanding bugs cursing the program. Blu-ray (BD-J) menus seem to work as intended now, even though things are a bit rough with Ultra HD Blu-ray discs according to some brief tests conducted with recently purchased releases.
Finally, the new VLC includes fixes for multiple security issues, which are detailed on the latest official security bulletin. The fixed bugs include a denial of service issue that could be triggered with a wrong mp4 file (div by 0) (#27202), some crashes with multiple files due to double free (#26930), a denial of service issue that could be triggered with a wrong oog file (null pointer dereference) (#27294) and a potential buffer overflow in the vnc module that could trigger remote code execution through a malicious vnc URL (#27335, CVE-2022-41325).
The four patched vulnerabilities could have been used by a malicious third party to trigger either a crash of VLC or an arbitrary code execution with privileges. There are no known exploits performing code execution through these vulnerabilities, VideoLAN said.











