[ad_1]
The benefit proposition for the products and services in the EM+S E5 suite does not look like it has been convincing to buyers for a although now. Over the past calendar year or so, Microsoft has been putting a large amount of perform into the Defender companies to increase that value proposition, and to deliver a improved complex security resolution for Microsoft 365 buyers.
In the final yr or so Microsoft has rebranded and reorganized the Defender programs into Defender for Cloud Applications, Defender for Workplace 365, Defender for Endpoint, and Defender for Id. Although those people four companies are a superior begin, there are still gaps in the defense they supply.
To that end, Microsoft has added a new products in general public preview to the Defender Suite, Microsoft Defender Vulnerability Administration (DVM). DVM is focused at improving vulnerability administration in the following parts:
- Security baselines assessment
- Browser extensions evaluation
- Digital certificates assessment
- Network shares assessment
- Blocking vulnerable apps
- Vulnerability evaluation for unmanaged endpoints
In this website article we’re heading to search at the public preview for this new assistance. How to get it activated in your tenant, what it does, and the place I see it fitting into your total security architecture for Microsoft 365.
Activating the public preview
Whilst community previews for several new Microsoft 365 characteristics are automatically additional to tenants, the general public preview for DVW necessitates a limited approach to activate. You can indicator up in this article. That process only took me a few of minutes, then I experienced new licenses in my tenant that I could assign to an admin account to attain accessibility to DVM options. When that is complete, you will have accessibility to the feature we’ll go over below.
The place is DVM?
The GUI for the Microsoft 365 Defender stack of applications is generally (but not entirely) homed in the Microsoft Protection Portal. Even though this can make it a minimal tough to differentiate the operation of the different purposes inside of the Defender stack, it also provides us a “one cease shop” for Microsoft 365 stability configurations. Possibly a separate portal for just about every software would be a excellent thought, but then again perhaps this way is very best.
Once you have DVM licensed and you have logged into the Protection Portal, you will locate all the new DVM attributes available under the Endpoints area on the still left-hand facet of the display:
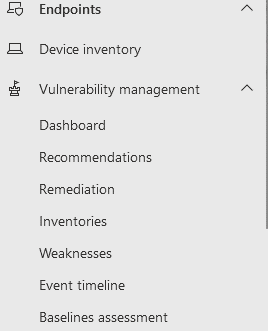
There are now seven subsections under Vulnerability Administration in this article. As this application is however in community preview, that may perhaps modify just before DVM hits GA.
Exploring the Dashboard and Suggestions
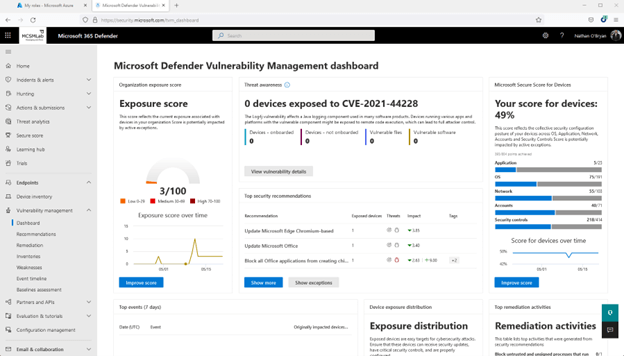
The to start with spot to discover is the dashboard. In this article you will locate a quick watch of a several different measures of vulnerability within just your Microsoft 365 tenant.
In my tenant, you can see my publicity rating is very low (3/100 is a superior factor. You want that selection to be as low as possible), and my secure rating for units is not terrific (49% indicates I have remediated about fifty percent of the troubles Microsoft screens to make up that score).
Clicking on Improve Score on either of people widgets will get you to the suggestions sub-part, where prompt remediations are comprehensive to enable you make improvements to the safety posture of your tenant.
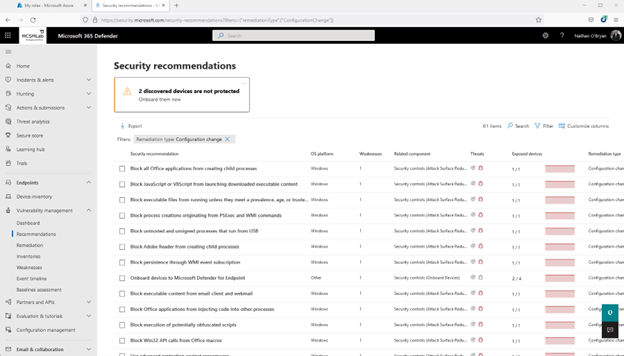
Under is a screenshot of the suggestions web page for my system protected score. With 61 goods to tackle, it appears to be like I have to some operate to do in my tenant.
Remediation
The remediation sub-part is for organizing the recommendations into active tasks.
Likely again up to suggestions for my safe rating for units, I picked a single of the suggestions (in this circumstance “Update Office”), and then picked the Ask for remediation button at the base of the fly-out web page.
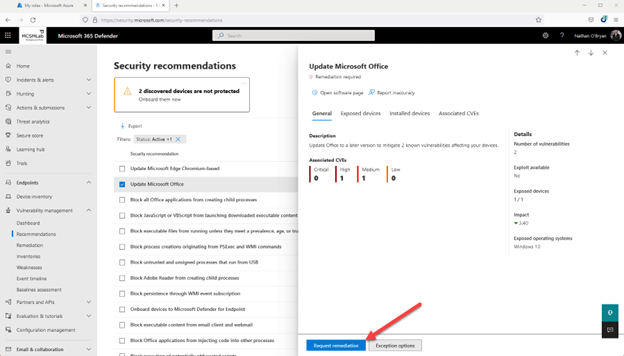
This will give you a speedy wizard that makes it possible for you to mark that recommendation for remediation. It’s by no signifies a full-blown ticketing process, but this seems like it could be handy for prioritizing the implementation of those people tips in your crew. Not super helpful for me, as I am the only administrator in my tenant.
Inventories
The inventories tab presents you an inventory of the programs, browser extensions, and certificates set up on Home windows machines that have been inventoried into Endpoint Management.
I do have an iPad that has Defender, but no purposes from that system are inventoried right here. This sub-portion will inventory macOS, Linux, and Home windows. iOS and Android equipment are left out for now.
Weaknesses
The weaknesses sub-portion is but one more see of the same details introduced in a different way. In this article you are going to see vulnerabilities that can have an affect on your devices mentioned by vulnerability title.
Below you can see I chosen a single of the vulnerabilities that is associated to Business. It displays me that I have a person Windows 10 laptop that wants an Workplace update.
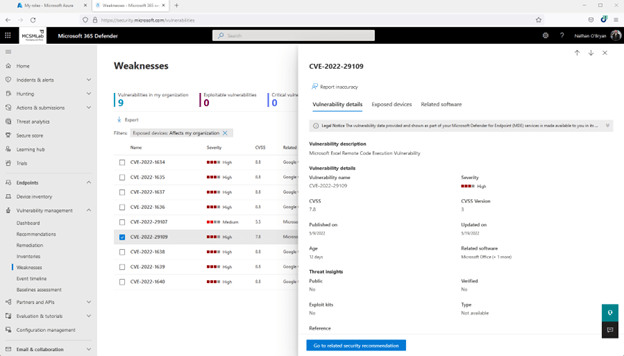
It is telling me that updating Business on that just one laptop computer will acquire care of the Recommendation, the Remediation that I opened from that Suggestion, and this Weak spot listed below.
When that amount of redundancy possibly isn’t required for a tiny tenant like mine, I do appear ahead to enjoying all-around with DVM in a substantially larger tenant. I imagine this information and facts would be substantially more handy in a more substantial surroundings exactly where it is additional tricky to preserve keep track of of the distinctive vulnerabilities impacting a deployment.
Celebration Timeline
Guess what’s in the Celebration Timeline sub-area. If you guessed a different see of the same vulnerabilities, then you just acquired a gold star for the working day.
In the screenshot beneath, you can see that I genuinely want to update Workplace on that laptop computer!
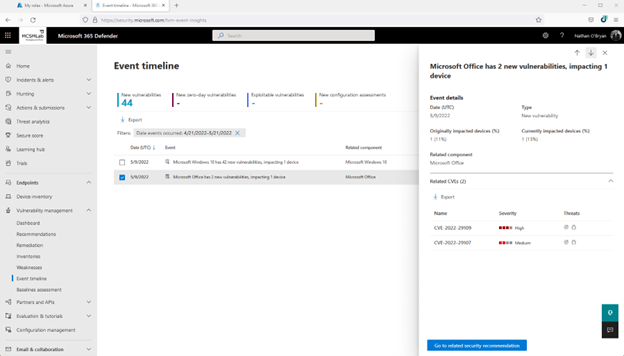
Again, this is the same two Place of work vulnerabilities that are shown in a somewhat unique see. There is even a button listed here that will acquire you back up to the Recommendations for these vulnerabilities.
Baseline Assessment
So much DVM has revealed us a dashboard that summarizes the vulnerabilities detailed in the future 5 sub-sections, then these similar vulnerabilities outlined in these five distinctive subsections. I never want to seem way too “complainy” below, as this is very good vulnerability details that can completely assistance directors improved protected their units, but I do feel these sub-sections could be condensed into a solitary pane with some sort of distinctive sights. I am not a UI designer, so probably there is a excellent reason Microsoft felt they wanted all that genuine estate inside the Stability Heart to current the identical details various periods.
The Baseline Evaluation sub-section, even so, does supply different performance. According to Microsoft Documentation:
“A protection baseline profile is a custom made profile that you can create to evaluate and keep an eye on endpoints in your corporation against market protection benchmarks. When you develop a safety baseline profile, you might be building a template that is made up of various system configuration options and a foundation benchmark to examine in opposition to.”
To produce a Baseline Assessment profile:
- From the Baseline Assessment sub-part, pick out “+Create” in the higher left to generate a new profile.
- Name your new profile and include a description. Pick out Following.
- Find your profile scope by deciding on software package to keep track of (Variations of Home windows 10 and 11 are shown right here. Ideally Microsoft will incorporate extra software program at a afterwards day), a baseline benchmark (I picked CIS v1.12.), and a compliance amount. Choose Subsequent
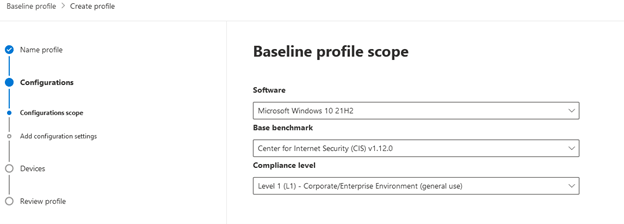
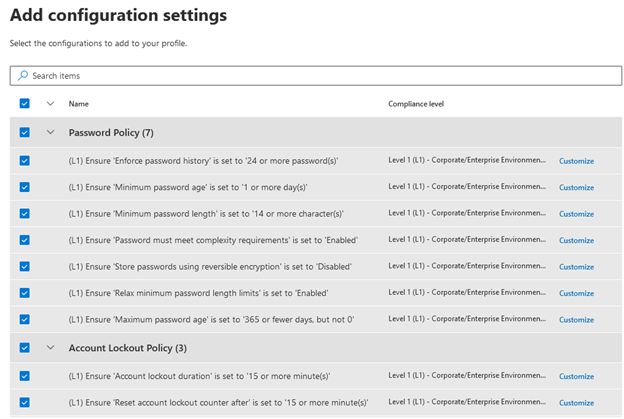
- Insert configuration settings. Dependent on the benchmark and compliance level selected on the very last web site, you will see distinct configuration options you can select. With the picks I produced there are hundreds of distinct configuration configurations for me to select from. I’m likely to choose them all for this test profile, but you’ll want to devote some time on deciding on choices that meet your organization’s compliance demands. There is also a Customise button to the appropriate of each individual environment so you can edit every environment separately. After you are accomplished, pick Up coming.
- Opt for gadgets to assess. I only have a person system in my tenant to which this profile can utilize, so I chosen All system groups. Choose Up coming, then overview you profile options on the following page and post the profile. The moment you have submitted your bassline assessment profile, it will consider some time for any new facts to show up. The documentation states 12 hours.
I’m going to enable that run, then we’ll get a deeper seem at the baseline assessment and around DVM characteristics in a foreseeable future blog site article.

With electronic mail getting one particular of the most mission-important instruments for companies nowadays, how do you ensure critical enterprise interaction stays up and jogging? How do you display to senior administration that further resources are essential to meet up with growing desire or that company stages are getting fulfilled?
Produced by Exchange architects with immediate products enter from Trade MVPs, ENow’s Mailscape would make your career much easier by placing almost everything you need into a single, concise OneLook dashboard, alternatively of forcing you to use fragmented and complex instruments for checking and reporting. Uncomplicated to deploy and intuitive to use, get started off with Mailscape in minutes rather than times.
Obtain YOUR Cost-free 14-Day Trial and incorporate all important features for your Exchange monitoring and reporting to maintain your messaging infrastructure up and operating like a pro!
Item HIGHLIGHTS
- Consolidated dashboard perspective of messaging environments wellbeing
- Immediately validate exterior Mail move, OWA, ActiveSync, Outlook Any where
- Mail move queue checking
- DAG configuration and failover monitoring
- Microsoft Security Patch verification
- 200+ constructed-in, customizable reviews, including: Mailbox dimension, Mail Visitors, Quota, Storage, Distribution Lists, General public Folders, Databases dimension, OWA, Outlook version, permissions, SLA and cell system studies
[ad_2]
Source connection









